An Important Way to Step Up Your Online Security Game
In one of my previous posts I discussed cloud services and some steps you can take to help remain secure while online. The goal of today's discussion is to select and emphasize one particular step: two-factor authentication.
Whoa, "two-factor authentication" sounds like too much for you to handle? Don't run away just yet. Two-factor authentication, hereafter referred to in this post as "2FA", is a simple concept. First observe the list of "authentication factors" below.
- Something you know
- Something you have
- Something you are
We are used to authenticating ourselves with one thing - a password. Passwords are (usually) memorized and therefore are considered something we know. The downside to this approach of using a single factor is that anyone who can guess what you know can pretend to be you.
What if instead of just a password, you had to prove that you are in possession of something or that you are physically who you say you are? Many online services offer 2FA in the form of registering something you have in your possession.
The most common second factor used is a phone number. The online service you attempt to log into will send you unique, one-time codes to your phone number by either text message or phone call and will require that you enter the code you received each time you log in. The main drawback of using a phone number as a second factor is that incoming texts and phone calls to your mobile are susceptible to be intercepted or redirected by a malicious actor.
The other common second factor used is a security token. A security token can be an app installed on your phone or computer, or it can be a USB device similar to a flash drive attached to your computer.
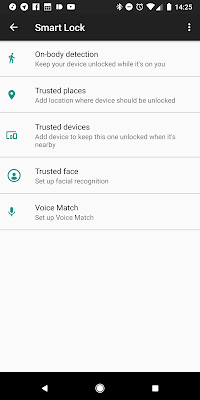
One method that is becoming more common is known as push authentication. Google is an example of a company that has implemented push authentication if you have a smartphone or tablet. Duo and LastPass have also implemented push authentication in their authenticator apps. The main benefit of push authentication is that it is quick and user-friendly. When you sign into your account, instead of having to enter a code, you will simply be required to approve the login via a push notification on your smartphone where the authenticator is installed.
The image below is what I'm presented with whenever I attempt to sign into my Google account on a new device.
If I tap "yes", my sign-in completes and I'm good to go. If someone were to steal my password and attempt to log into my account, they would also have to steal my phone and bypass my phone's lock code to successfully log in. The possibility of that happening is very slim. Besides if my phone were stolen, the first few things I would do are trigger a remote data wipe, change my account passwords, and invalidate any existing login sessions to my Google account.
The big social media sites support adding 2FA to your account, and I highly recommend it. You should also enable it on any email services you use and banking or financial services. What a thief usually wants to do with your information is get to your money, your identity, or get to other people through you. Enabling 2FA on your accounts will add a significant amount of difficulty for anyone looking to compromise your online presence.
If you have questions about anything discussed above or how to enable 2FA on a specific service, feel free to contact me.
If you have questions about anything discussed above or how to enable 2FA on a specific service, feel free to contact me.





Comments
Post a Comment