Cloud Services - Friend or Foe?
The question has arisen many times in my profession, and my friends and family have even asked me:
"Is it safe to store this information in the cloud?"To answer this question, we need to understand what the cloud is. Then we need to determine what kind of information you intend to store, and how important it is that the information remain private.
The "cloud" - what does this nebulous term mean?
Understanding the cloud
Let's make sure we understand what the cloud is not. You're reading this article on a device such as a smartphone, personal computer, or tablet. Your device is not part of the cloud, but it is a client of a server that is part of the cloud.
As an aside, things can happen that can change this "default" behavior of your personal device, and it's generally not a good idea to change it if you don't know what the implications are.
Popular cloud storage providers:
Not long ago a recruiter asked me to email them my name, date of birth, and social security number. I called the recruiter and explained that I wasn't comfortable doing that. Unfortunately some businesses will collect this information from employees and store it somewhere that isn't as secure as you would think, regardless of the measures you take to ensure it gets to them securely.
Have any cloud services ever been breached? The answer is a resounding yes; time and time again. Here's a short list of cloud-based companies who have reported breaches over the years:
Now you know a little bit more about the cloud and your responsibilities with it. Do you trust it enough to use it? I have found that the benefits of cloud services for my personal use have outweighed the risks. Let me know your thoughts in the comments below.
A word on client vs server
Suppose you go to your neighbor's house and knock on the door, but no one answers. Your neighbor wasn't expecting anyone, and they don't let strangers in. On the other hand if you visit a restaurant, usually a host or hostess will greet you and get you seated, then a server will bring you food and drink that you order. Restaurants are open to the public and are expecting people to come in and make orders. In the example, you represent the device you're using to read this article - you are a client. Your neighbor represents another device connected to the Internet. They may or may not be a client, but they have nothing to do with you. The restaurant represents a server somewhere on the Internet that holds a copy of my website. That server is expecting you to visit, and it presents my website to you. Your smartphone, computer, or tablet is not expecting visitors from the Internet, and therefore does not answer requests to open websites or other kinds of services.As an aside, things can happen that can change this "default" behavior of your personal device, and it's generally not a good idea to change it if you don't know what the implications are.
A formal definition
Now for the formal Dictionary.com definition of the cloud:Digital Technology. any of several, often proprietary, parts of the Internet that allow online processing and storage of documents and data as well as electronic access to software and other resources(usually preceded by the)One thing needs to be reiterated: being connected to the Internet does not automatically make you part of the cloud, but you are most likely heavily relying on cloud services. Cloud storage, cloud computing, cloud computing infrastructure and hosting are the most popular terms used to describe cloud services.
- Cloud storage is self-descriptive; you store your data there.
- Cloud computing is a more broad term that refers to not only storage but processing of data in the cloud.
- Cloud computing infrastructure is a specific term for the elements of IT infrastructure that exist in the cloud, usually for providing it as a service.
- Hosting refers to maintaining servers for customers to use to serve their data.
In the business world, more technical terms are used including IaaS, PaaS, and SaaS. For more details on those terms, read here.
The business entity that provides the service is known as the Cloud Service Provider (CSP).
The business entity that provides the service is known as the Cloud Service Provider (CSP).
Examples of cloud companies and services
Popular cloud storage providers:
- Google Drive
- Dropbox
- Box
- Microsoft OneDrive
Popular hosting providers:
- Amazon
- HP
- IBM
- Microsoft
- Rackspace
All of the above are considered cloud computing companies.
Understanding the information
To whom does it belong? This should be the largest deciding factor in your decision. Maybe the information is solely yours, so you have more freedom with where and how you store it. If you're doing business with customers, however, here's where things get interesting. You are legally bound to secure your clients' digital information. The main categories of protected information are as follows:
- PII - Personally Identifiable Information - popularly defined by NIST SP 800-122
- PHI - Protected Health Information - outlined in HIPAA
- PCI-DSS - Payment Card Industry - Data Security Standard - maintained by a council
If you collect any of the above types of information in the course of business, you're bound by one of several laws to maintain the security of that information. Don't forget the ethical obligations as well. Hospitals and banks, especially, have rigorous requirements as to how they store and transfer protected information.
However, just because the legal requirement exists does not mean they are compliant. Audits are performed and fines are issued for noncompliance. Some CSPs (cloud service providers) are attested to conform to compliance regulations - these should be at the top of your list of potential choices. For more details, look into the ISO27k family of standards.
However, just because the legal requirement exists does not mean they are compliant. Audits are performed and fines are issued for noncompliance. Some CSPs (cloud service providers) are attested to conform to compliance regulations - these should be at the top of your list of potential choices. For more details, look into the ISO27k family of standards.
Importance of information
Is the information you want to store important? It most likely is since you're looking to store it in a duplicate location (somewhere other than your computer). Of equal importance to making sure the data is not lost entirely is making sure the data is not stolen or treated as public knowledge if it should remain private. You wouldn't post a picture of your credit card or social security card on Facebook, so don't ask someone to email you their name, phone number, address, credit card number, etc.Not long ago a recruiter asked me to email them my name, date of birth, and social security number. I called the recruiter and explained that I wasn't comfortable doing that. Unfortunately some businesses will collect this information from employees and store it somewhere that isn't as secure as you would think, regardless of the measures you take to ensure it gets to them securely.
The weakest link is the best target
Note that it doesn't matter where the information is stored if the account or computer that accesses it becomes compromised. Among the general public, it's more likely for data to be lost or stolen as a result of malware infection or social engineering attack (e.g. phishing), or a combination of the two, than for the data to be leaked or breached by hackers.Have any cloud services ever been breached? The answer is a resounding yes; time and time again. Here's a short list of cloud-based companies who have reported breaches over the years:
We're not talking just a few, but millions of accounts compromised by these breaches, along with personal information including email addresses, passwords, and credit card information. Here's an article about some interesting security issues related to enterprise applications that use cloud services backends.
Understanding the Risk
It's very hard to predict the future (wouldn't that be nice, though?). Everyone who uses cloud services (storage or compute) must accept a level of risk. In the information security realm, we often talk about risk management - reducing risk (risk mitigation) to an acceptable level (risk acceptance). Cloud service companies often will promise you via a publicly disclosed privacy policy that they are committed to the security of your information. Take a look at one of the largest cloud service company's policies.Steps you can take
Should you decide to opt-in to using cloud services to store your information, here are some steps you can take to reduce the risk of your sensitive information becoming compromised:- Use secure, unique passwords
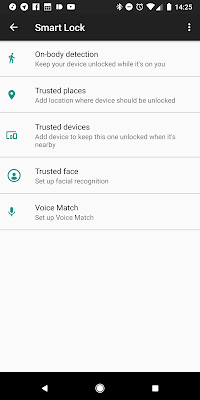
- Use two-factor authentication
- Do not email or text sensitive information. Use secure file-sharing services like Citrix ShareFile or Box. For secure messaging as a replacement for text (SMS), consider services like Telegram or WhatsApp.
- For businesses or individuals with elevated concerns: encrypt the data before transmission to the CSP; use strong encryption, strong keys, and secure key management.
Now you know a little bit more about the cloud and your responsibilities with it. Do you trust it enough to use it? I have found that the benefits of cloud services for my personal use have outweighed the risks. Let me know your thoughts in the comments below.







Comments
Post a Comment